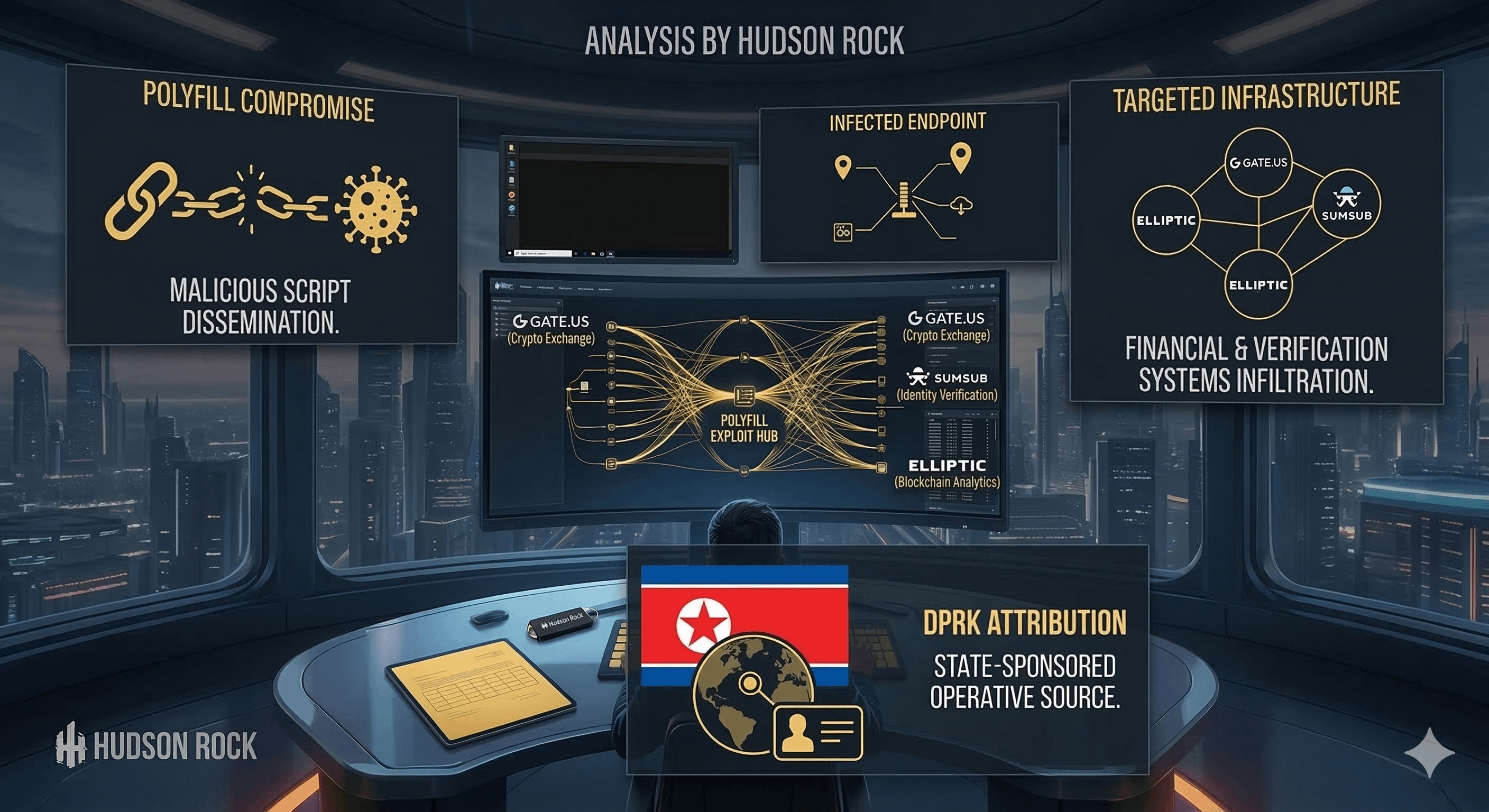
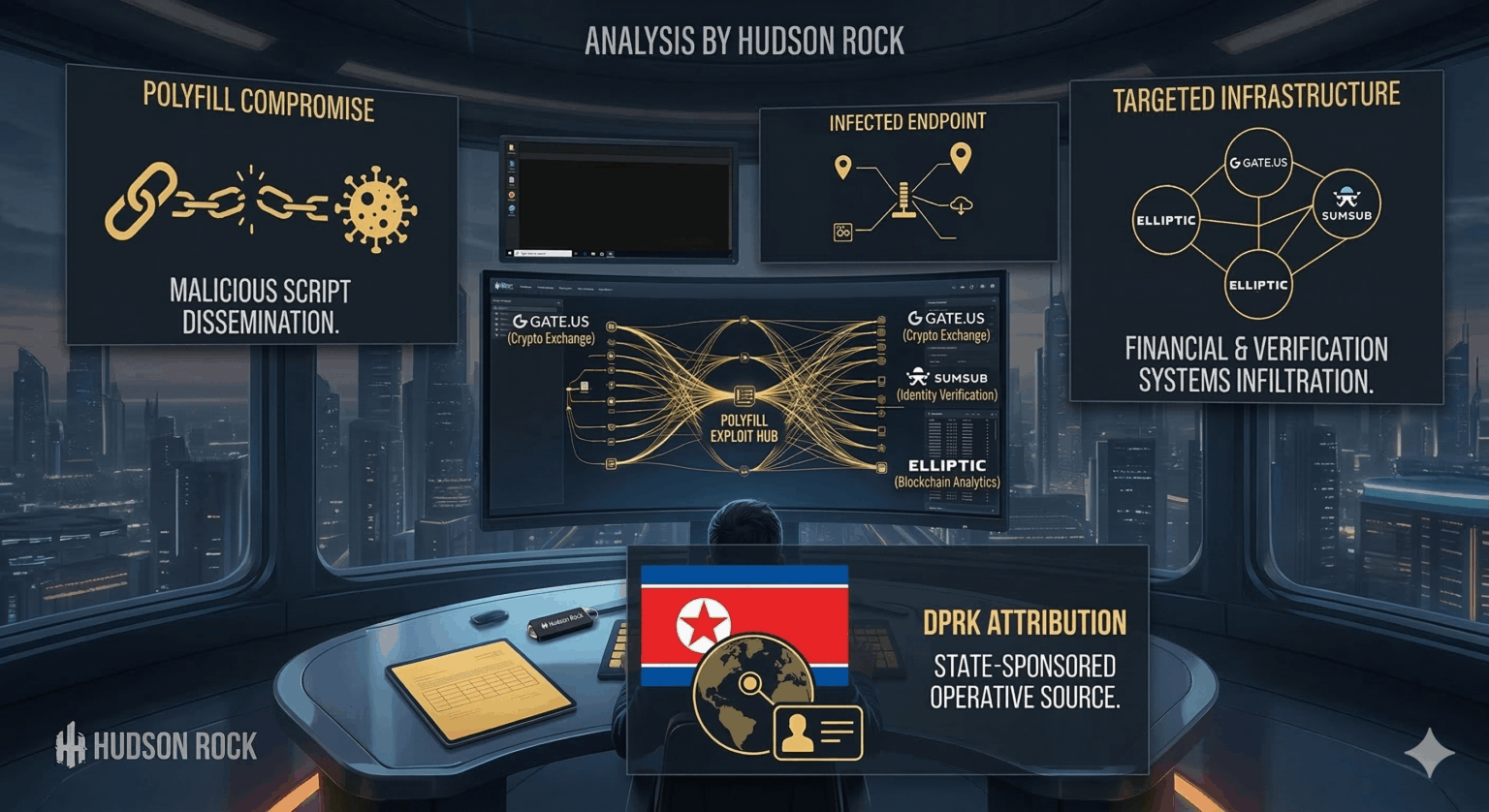
Uncovering a crazy story where a North Korean was hired to work at major crypto exchange gate(.)us and literally tapped into calls with identity verification firm, Sumsub, and blockchain Analytics firm, Elliptic, where they designed the KYC/AML procedures meant to stop North Korea from laundering funds using Gate(.)us.
This allowed them to reverse-engineer the exchange's compliance logic. He was even testing the system using the profiles of real FBI fugitives to find blind spots.
Automated Laundering: The operative built a Telegram-based bot to automate USDT washing, utilizing TRON "energy lending" mechanisms to slash transaction fees by 85% while moving illicit funds.
1 Comment
tldr; An infostealer infection exposed a North Korean operative involved in global cyber espionage and supply chain attacks. The operative infiltrated U.S. crypto exchange Gate.us, participated in AML/KYC compliance meetings, and was linked to the Polyfill.io supply chain attack, which compromised over 100,000 websites. The infection revealed operational data, including credentials and communications, tying the operative to North Korean state-sponsored activities and a Chinese syndicate. This highlights the convergence of cybercrime and state espionage.
*This summary is auto generated by a bot and not meant to replace reading the original article. As always, DYOR.